Extending Identity Based Policies to Cisco Firepower
At Entek IT, we engage with a diverse range of products within Cisco’s networking portfolio. Our expertise includes implementing Cisco solutions that facilitate the establishment of networking security policies grounded in endpoint identity. We often encounter the need to broaden the Identity-Based Policy domain beyond Cisco’s SD-Access (SDA) technology as part of a Zero Trust approach. In this blog post, we delve into the extension of identity-based policies to Cisco’s Firepower firewalls, which are integral components of many customers' networking infrastructures.
What are we looking at?
Organisations require the seamless extension of identity-based network segmentation from Cisco's SD-Access to other infrastructure elements, such as Cisco Firepower firewalls. This extension is essential for maintaining consistent policy enforcement and visibility across the network infrastructure, which is a vital element in a Zero Trust architecture approach.
The Challenge
The technical challenge lies in devising a solution that not only integrates Cisco's SD-Access identity-based network segmentation with Cisco Firepower firewalls but also ensures network availability. This integration must provide smooth policy enforcement and uniform visibility across all network components while guaranteeing high availability, resilience, and operational continuity under diverse conditions.
The Solution
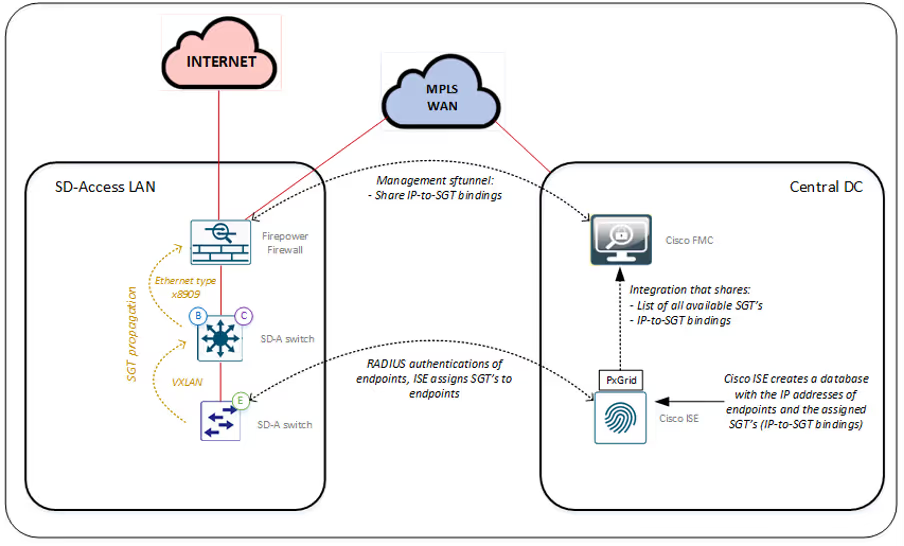
Cisco Identity Services Engine (ISE) serves as the central component for authenticating endpoints connecting to the network. As part of this authentication process, Cisco ISE assigns an authorization profile to authenticated endpoints. One aspect of this solution within Cisco ISE is TrustSEC.
When an endpoint connects to the SD-Access switch, the switch assigns a Scalable Group Tag (SGT) to the authentication session. This identity information enables the application of security and networking policies tailored to the specific endpoint traffic.
Cisco Firepower Firewalls, responsible for connecting and safeguarding the SD-Access LAN, can also support the TrustSEC solution. Once these firewalls are aware of the identity information associated with specific traffic, policies can be enforced accordingly. This capability allows Firepower Firewalls to apply Identity-Based policies to the traffic they forward.
The Firepower Firewalls employ two technical methods to obtain identity information for the application of Identity-Based policies to traffic; inline propagation of identity information and exchanging identity information through integration.
Option 1: Inline Propagation of Identity Information
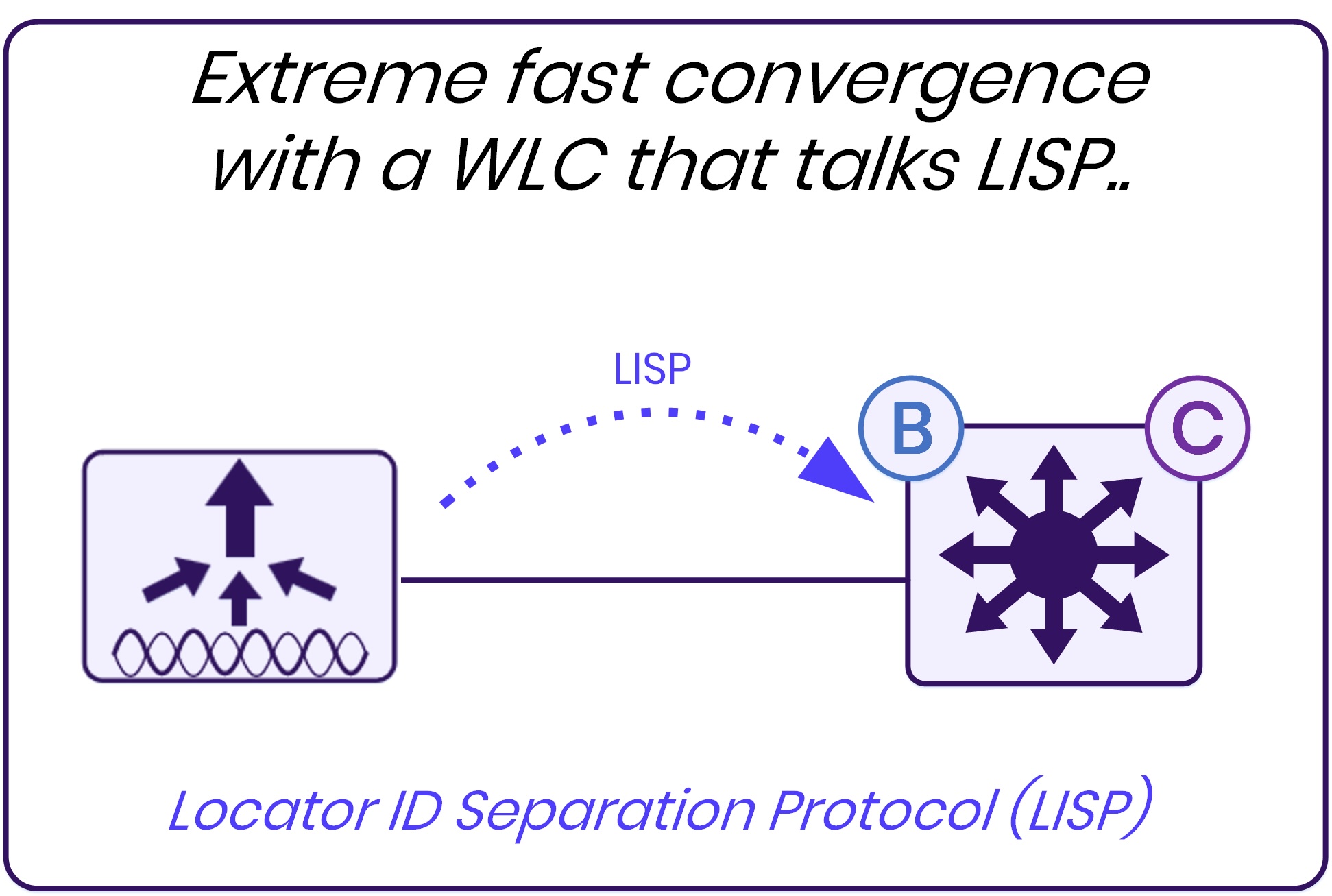
In Cisco’s SD-Access solution, VXLAN encapsulation is utilised in the data plane to facilitate traffic forwarding among SD-Access networking components such as switches and wireless APs. The VXLAN header incorporates SGT information, ensuring that every packet transmitted within the SD-Access fabric is tagged with the assigned identity information.
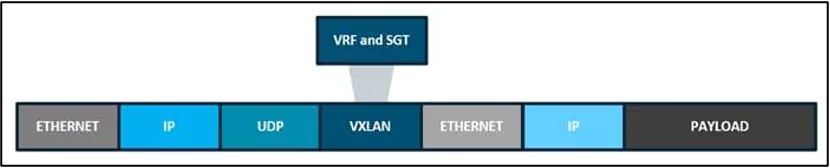
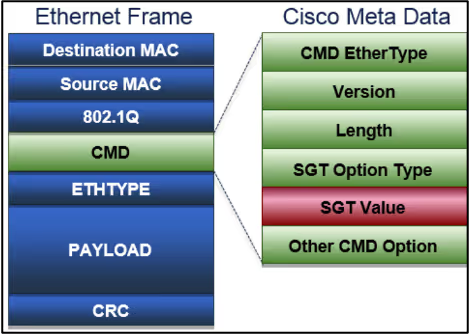
However, Cisco Firepower Firewalls cannot be seamlessly integrated into the SD-Access fabric with VXLAN and LISP. To ensure that traffic originating from the SD-Access fabric towards the Firepower Firewalls includes identity information, a different protocol can be employed. The Etherframe type x8909, an extension of the normal Ethernet protocol with the addition of the Cisco Metadata Header (CMD), facilitates the storage of SGT information within the header. Both Cisco Catalyst switches and Firepower firewalls support this etherframe type.
Option 2: Exchanging Identity Information Through Integration
Cisco ISE serves as the central component for authenticating and authorizing endpoints on the network. Given its capability to assign identities to endpoints, Cisco ISE maintains awareness of the IP-to-SGT mappings, associating endpoint IPs with their respective assigned identities. This information is stored within Cisco ISE's database and can be shared with external solutions through Pxgrid.
Cisco Firepower Management Center (FMC) acts as the orchestration platform responsible for managing Firepower firewalls. Through integration with Cisco ISE using Pxgrid, Cisco FMC facilitates the exchange of crucial information, including:
- IP-to-SGT bindings utilizing a publisher/subscriber information sharing model.
- A comprehensive list of identities, encompassing SGTs created within Cisco ISE.
The information received from Cisco ISE via Cisco FMC is then relayed to the Firepower firewalls under its management. This mechanism enables Firepower firewalls to gain awareness of the IP-to-SGT bindings maintained by Cisco ISE. Consequently, this information empowers Firepower firewalls to construct identity-based policies, as they can now discern traffic associated with specific identities.
The schematic representation of this concept is depicted in the figure below.
Our experience
Throughout our journey, we've closely collaborated with Cisco on this crucial topic, witnessing the evolution of these features over time. Our team at Entek IT has successfully implemented both options discussed in this blog in many deployments.
In our approach to designing Cisco SD-Access solutions, we prioritise embedding the identity-based concept into our designs by default. This proactive stance ensures that identity-based policies are seamlessly integrated into the fabric of our solutions, enabling enhanced security and efficiency.
With the advancements in newer Firepower software, new capabilities have emerged, including the ability to construct traffic steering policies based on identity, exemplified by Direct Internet Access (DIA) policies. Additionally, the incorporation of policy-based routing based on Scalable Group Tags (SGT), introduced in version 7.4.0, further amplifies the flexibility of using Firepower firewalls in SD-Access networks.
If you're considering implementing identity-based policies within your network, don't hesitate to reach out to our team at Entek IT.