Identity PSK: Securely managing IOT devices
In today's hyper-connected campus networking environments managing secure access to wireless networks is more crucial than ever. Developments like the growing number of connected IOT devices increase the challenge to keep secure access manageable and accountable. With the use of Cisco's Software-Defined Access (SDA) solution, integrated with Identity Services Engine (ISE) and Catalyst Wireless, utilising Identity PSK (IPSK) can streamline and fortify secure network access management. This article explores the benefits of IPSK, its operational dynamics, and the synergies with Cisco ISE's role-based access control (RBAC) functionalities.
Benefits of IPSK
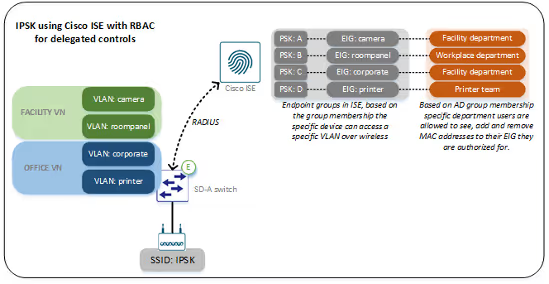
IPSK is regarded as a significant enhancement over traditional Pre-shared Key (PSK) by allowing networks to use a single SSID to connect multiple endpoints to their respective VLANs through unique PSKs. This approach simplifies the wireless network infrastructure by reducing the number of SSIDs, thereby decreasing the administrative overhead, and improving wireless airtime efficiency due to fewer broadcast and management frames.
The primary advantage of IPSK is its capability to offer differentiated access to devices with minimal configuration changes. Each endpoint device (group) is assigned a unique PSK that determines its network access privileges. This not only simplifies the management but also elevates security by isolating endpoint devices in distinct VLANs as per their credentials, preventing lateral movement in case of a security breach.
IPSK can enhance operational efficiency by providing the delegation of network management tasks to authorised roles or stakeholders within an organisation. In other words, specific stakeholders can be identified which are given the ability to manage and control the secure access of for example IOT devices within the organisation. This delegation of control can expedite processes, lightens the workload of central IT, and allows them to concentrate on strategic initiatives. Additionally, it lowers operational costs by streamlining the management of network endpoints and facilitating easier scaling as the number and variety of endpoints will continue to grow.
How IPSK works
IPSK combined with Cisco’s ISE and Catalyst wireless products provide a robust and flexible framework for managing access. Here’s a closer look at the setup:
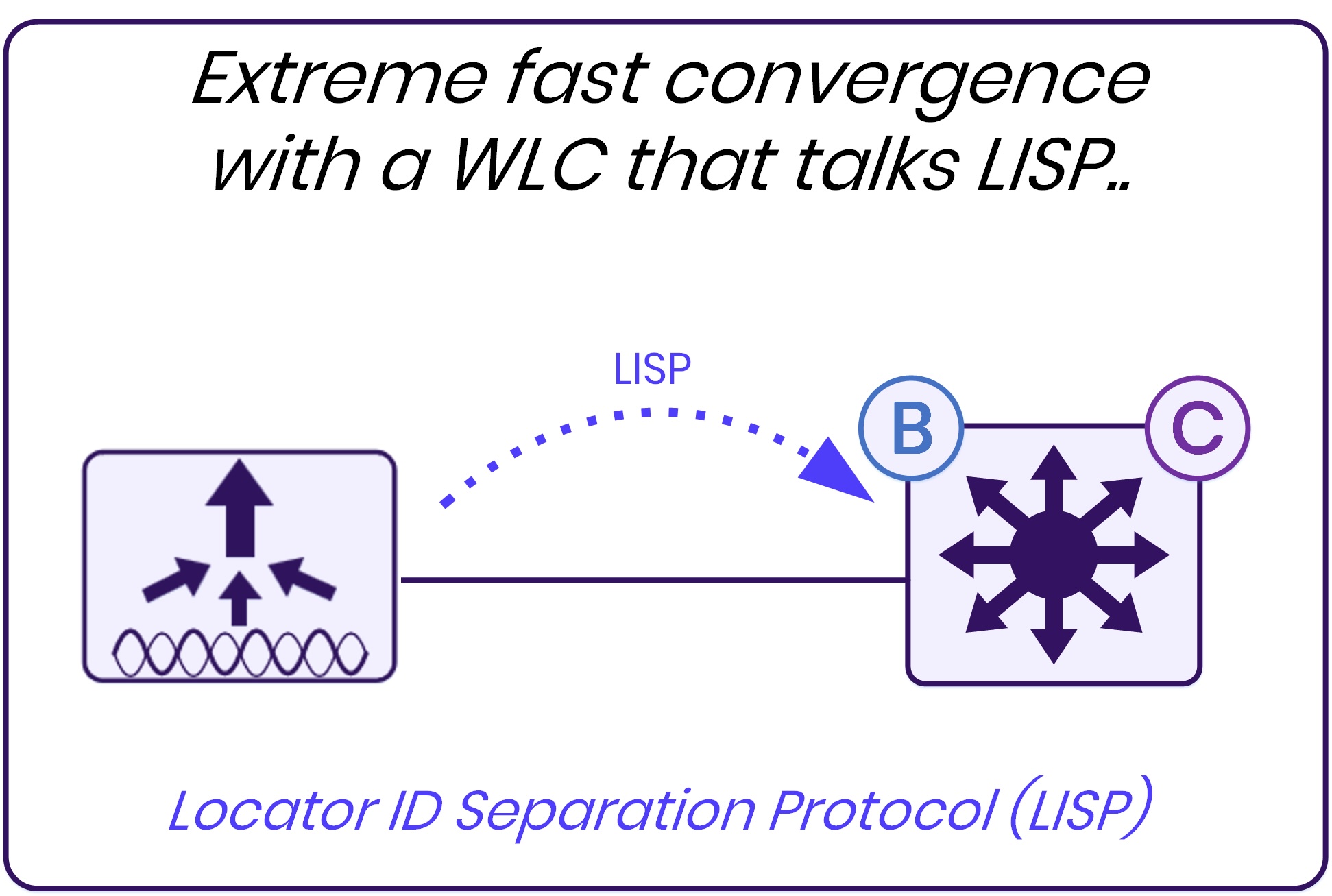
- Wireless setup: In the Cisco wireless network setup for enabling IPSK, the administrator must configure the WLAN to use PSK authentication. This is achieved by setting up the Wireless LAN Controller (WLC) to handle PSK authentication specifically for the designated SSID. Additionally, MAC address bypass must be enabled on the SSID, ensuring devices are authenticated based on their MAC address as part of the IPSK configuration process.
- Cisco ISE setup: When a device connects to the IPSK enabled SSID, the authentication attempt is forward to Cisco ISE using RADIUS. Based on the MAC address membership, Cisco ISE returns the VLAN and PSK which will be assigned and matched by the WLC.
Extending IPSK
Cisco ISE's RBAC functionality can be integrated with IPSK to streamline the management of providing secure access to devices. RBAC allows network administrators to delegate specific authorization responsibilities to different roles and stakeholders within an organisation. They can be enabled to manage the PSKs and associated VLAN assignments for their respective departments. Practically, this can result in a scenario where non-IT staff can add (or remove) IOT devices to the network by adding a MAC address to a specific group.
In order to achieve flexibility and increase the agility to deploy new identities, we recommend building a generic network/VN in Cisco SDA and assign all IPSK identities to this network. Use Cisco TrustSec to determine which identity is allowed to access certain resources and other identities on the network. The security policies for this setup can be further enhanced by utilizing Cisco Firepower firewalls that can be integrated with Cisco ISE and therefore further limit access based on identities (not source IPs). See our previous blog “Extending Identity-Based Policies to Cisco Firepower Firewalls” for more details.
Our Experience with IPSK
We have deployed IPSK as described in this blog for various customers. We have seen that the described deployment helps organisations in their challenge to quickly and securely allow IOT related devices on the network, while at the same time delegating control to stakeholders, off-loading the IT team. In one scenario, we have created a solution to deploy IPSK without the need for MAC registration, which fulfilled the wish to enter the specific PSK on a device to grant access to the associated VLAN.
Looking to solve your secure network access challenges for IoT devices? Implementing IPSK could be your answer. Reach out to discover implementation options for your network.